Protonyte Penetration
Testing Services
critical risks giving clarity to teams, confidence to leaders, and assurance to the board.
Home ➔ Penetation Testing
What is Penetration Testing ?
Penetration Testing is a security assessment process where ethical hackers simulate real cyberattacks to identify weaknesses in your systems. It helps organizations understand how attackers could gain unauthorized access and provides insights to fix vulnerabilities before they can be exploited.
By testing networks, applications, and devices under real-world conditions, pentesting ensures your defenses are strong, updated, and capable of protecting critical data.
Key Highlights
Simulates real cyberattacks performed by ethical hackers
Identifies vulnerabilities in networks, applications, and systems
Helps prevent unauthorized access and data breaches
Strengthens overall cybersecurity readiness


Why Your Business Needs Penetration Testing
Penetration Testing is essential for safeguarding your business against modern cyber threats. It helps you uncover hidden vulnerabilities before attackers can find and exploit them. By simulating real-world attacks, pentesting provides a clear view of your actual security posture and ensures your systems, data, and operations remain safe.
Regular pentesting not only protects your business but also builds customer trust, strengthens compliance, and reduces the chances of costly security incidents.
Key Benefits
Identifies security gaps before hackers can exploit them
Protects sensitive business and customer data
Ensures compliance with industry and regulatory standards
Enhances your overall cybersecurity strength
Web Penetration Testing ?
Web penetration testing provides a complete security assessment of your website and web applications by simulating real-world cyberattacks. Ethical hackers analyze your systems from an attacker’s perspective to identify hidden weaknesses that could lead to data breaches, unauthorized access, or service disruption.
This process uncovers critical issues such as injection vulnerabilities (SQLi, XSS), broken authentication, insecure configurations, exposed sensitive data, weak session management, outdated components, and insecure API endpoints.
After the assessment, you receive a detailed report that clearly outlines each vulnerability, its severity, potential impact, and expert recommendations—allowing your team to prioritize and fix risks effectively.

Mobile Penetration Testing ?
Mobile penetration testing evaluates your Android and iOS applications using real-world attack techniques to uncover hidden security weaknesses that could put user data or your system at risk. Ethical hackers thoroughly assess the app’s frontend, backend, APIs, data storage, permissions, encryption, and network communication.
This process identifies critical issues such as insecure data storage, weak authentication, poor session management, insecure APIs, outdated libraries, reverse-engineering risks, malware injection possibilities, and unauthorized access paths.
After the assessment, you receive a detailed report that clearly highlights each vulnerability, its risk level, potential impact, and actionable recommendations—helping you fix issues quickly and effectively.

BLACK BOX
Value: Black box pentesting service simulates a real-world attack and helps identify technical vulnerabilities and human-related security issues

GREY BOX
Value: Gray box pen testing service is the golden mean between quality and price. It’s cheaper and faster compared to the black box approach
WHITE BOX
Value: White box penetration test service allows you to detect hidden vulnerabilities that may go unnoticed during other types of pentests
Penetration Testing
Penetration Testing ek controlled cyber attack hota hai jisme ethical hackers real-world attackers jaisi techniques use karke system, website, network, ya application me security weaknesses identify karte hain. Iska purpose damage karna nahi, balki organization ko strong & secure banana hota hai.
Why Penetration Testing is Important?
Attackers se pehle vulnerabilities identify ho jati hain
Organization ki security posture improve hoti hai
Data breaches ka risk kam hota hai
Compliance requirements (ISO, PCI-DSS, GDPR) meet hotay hain
Business trust & credibility increase hoti hai

Comprehens Cyber
Security Solutions Business
Protecting data, networks, and systems from cyber threats Lorem ipsum dolor sit amet, consectetur.
Desktop App Penetration Testing
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.

Mobile Applicaiton
Testing
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.

Mobile Applicaiton
Testing
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.
Network Security
Testing
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.
Desktop App Penetration Testing
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.

Mobile Applicaiton
Testing
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.

Mobile Applicaiton
Testing
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.
Network Security
Testing
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.
Friday, october 3, 2025
Reconnaisssance
Reconnaissance is the first phase of our cybersecurity assessment timeline. In this stage, we carefully collect publicly available and technical information about the target systems to understand th attack surface. This helps us identify potential entry points without actively exploiting the system, ensuring a safe and controlled assessment.
Key Activities Include:
Domain & IP information gathering
Technology stack identification
DNS, subdomains & network footprint analysis
Public exposure & digital footprint review
Reconnaisssance
Vulnerability Analysis
Friday, october 3, 2025
Vulnerability Analysis
Vulnerability Analysis is a critical phase in our cybersecurity assessment timeline. In this stage, we analyze systems, applications, and network components to identify security weaknesses that could be exploited by attackers.
The goal is to detect, validate, and prioritize vulnerabilities based on their risk and impact.
Key Activities Include:
Automated & manual vulnerability scanning
Misconfiguration analysis
Known CVEs identification
Risk severity assessment (Low, Medium, High, Critical)
False positive validation
Friday, october 3, 2025
Exploitation
Exploitation is a focused phase in our cybersecurity assessment timeline. In this stage, identified vulnerabilities are safely and ethically exploited to verify their real-world impact. This helps demonstrate how an attacker could gain unauthorized access while ensuring no damage to systems or data.
Key Activities Include:
Exploiting validated vulnerabilities
Gaining controlled access to systems
Privilege escalation testing
Proof-of-concept (PoC) development
Impact verification without disruption
Exploitation
Reporting
Friday, october 3, 2025
Reporting
Reporting is the final and most critical phase of our cybersecurity assessment timeline. In this stage, all findings are clearly documented with evidence, risk ratings, and actionable remediation steps. The report provides management and technical teams with a complete understanding of security risks and how to fix them.
Key Activities Include:
Detailed vulnerability documentation
Risk severity & business impact analysis
Proof-of-concept evidence (screenshots, logs)
Clear remediation & mitigation recommendations
Executive summary for decision-makers
We Use Reliable and Effective Tools

OWASP ZAP

BURPESUIT

ARACHNI

SONAR QUBE

SEMGREP

SYNK

NMAP

WAPPLAZER

KALI LINUX

PARROT SECURTIY
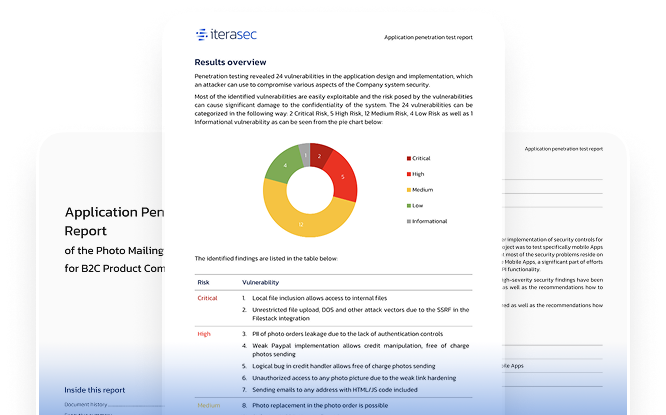
Explore our sample penetration testing service report
Please contact us, and we will send you a sample pentest report covering several applications.
Request Your Free Security Assessment
Have questions ? Let's talk.
other types
Different Types of Web Application Penetration Testing
At QuaLSec, we offer a range of penetration testing approaches to suit your
specific needs. Each type offers unique benefits.

Black Box Testing
This method simulates an external attacker without insider knowledge. It evaluates your application’s real-world defense system against unknown threats.

White Box Testing
In this comprehensive approach, our team works with complete access to your app’s codebase and structure. This thorough evaluation helps identify hidden weaknesses and potential logical errors.

Gray Box Testing
This testing technique combines both methods considering that limited internal information is available. This balanced approach offers complete security insights while replicating the actions of a partially informed attacker.
Group-IB Threat Intelligence
solution is ranked as one of
the best in class by Gartner,
Forrester, IDC and other
analysts

Digital Safety .
Data Privacy .
Secure Systems .
Threat Protection .
Risk Management .
Cyber Defense .
Threat Protection .
Get Fort and Create a
Professional Website Today!
Experinece The Mounnt in Mothion
During DDoS resilience testing, your web app or infrastructure is subjected to various real DDoS scenarios in order to identify weaknesses in protection at various levels of the system, including the network and application levels. This testing lets you to determine the current load limits and check the effectiveness of your anti-DDoS measures
Experinece The Mounnt in Mothion
During DDoS resilience testing, your web app or infrastructure is subjected to various real DDoS scenarios in order to identify weaknesses in protection at various levels of the system, including the network and application levels. This testing lets you to determine the current load limits and check the effectiveness of your anti-DDoS measures
Experinece The Mounnt in Mothions
During DDoS resilience testing, your web app or infrastructure is subjected to various real DDoS scenarios in order to identify weaknesses in protection at various levels of the system, including the network and application levels. This testing lets you to determine the current load limits and check the effectiveness of your anti-DDoS measures
Experinece The Mounnt in Mothion
During DDoS resilience testing, your web app or infrastructure is subjected to various real DDoS scenarios in order to identify weaknesses in protection at various levels of the system, including the network and application levels. This testing lets you to determine the current load limits and check the effectiveness of your anti-DDoS measures
Customer Case Studies
threats before they spread.
